5: Identity & Access Management
-
processes and procedures, and tools and tech used to oversee and manage digitial identities
-
goal is to provide secure and auditable access to digital resources of the organization
-
revoloves around IAAA
- identity
- authentication
- authorization
- auditing / accounting
authorized users gain access through identification, authentication and authorization
-
identification
- an individual makes a claim about an identity
-
authentication
- individual proves identity to the satisfaction of the access control system
exam tip:
remember that identification and authentication are separate and distinct steps! -
authorization
- indidvidual is allowed to access the system and/or resources
-
example:
- identification → username
- authentication → password
- authorization → access control list
-
accountability
- tracks user activity
-
authentication, authorization and accountability are known as AAA
-
note that it’s important that IAM systems work across cloud and on-prem environments
- process of making a claim
- public information
- identification must be unique
- standard naming convention should be used
- identifier shouldn’t contain extra information about the user
identification mechanisms uniquely identify each user of a system
- usually easily identify an indvividual
- commonly
flast, i.e.jmckenna - shouldn’t be considered secret
-
often proof of employment
-
may perform identification and authentication
-
magnetic stripe cards
- easily duplicated
- not secure
-
smart cards
-
more difficult to forge
-
has a chip
-
card readers
- read chip on the card
-
-
proximity cards
-
placed near reader
-
passive cards
- must be places inside the reader
- powered by the reader
* active cards - contain batteries
-
no matter what tech used for access cards, they must uniquely identify the user
-
-
uses the idea of “something you are”
-
good biometric systems provide
- easy enrollment
- low false acceptance rates
- low false rejection rates
- low intrusiveness (“creepy factor”)
- often found on devices
- iPhone, iPad, laptops, etc.
- allow for self-enrollment
- low false acceptance
- low false rejection
- analyze color patterns of the iris
- analyze blood vessels of the retina
- seen as intrusive by some users
- requires users to speak a phrase
- are subject to replay attacks
- often combined w/ other authentication techniques
- scans a user’s facial structure
- can be seen as intrustive to some users
- error rates are improvinig
- vein pattern analysis
- gait analysis
- hand geometry analysis
establishes an individual’s identity and creates their system account
-
request
request is made for a new identity, usually by someone like a hiring manger -
approval
request is approved for the new identity, usually by someone like a HR or department manager -
identity proofing
requested user is investigated, usually by an org registration authority -
issuance
the new identity is created, usually by a system admin
- separation of duties
- ideally all steps are completed by different individuals
- must be performed carefully
- use differing steps and documentation
- photo ID (Form I-9 approved documents)
- fingerprinting
- background checks
- proving an identity
- type 1: something you know
- type 2: something you have
- type 3: something you are
- type 4: something you do
“something you know,” knowledge-based, cognitive
-
normally a password
- strong passwords are long and complex
- passphrases are better
- easy to remember, hard to guess
-
answers to secret questions
-
password keys also provide knowledge-based authentication
“something you have”
- something you can touch
- requires physical posession of a device
- token devices, smart cards, memory cards, hardware keys, cryptographic keys, certificates, cookies
“something you are”
-
biometric authentication
-
static
- shouldn’t significantly change over time
- bound to a person’s physiological traits
- fingerprint, palmprint, hand geometry, iris, retina
- bound to a person’s physiological traits
- shouldn’t significantly change over time
-
dynamic
- based on behavioral traits
- voice, gait, signature, keyboard cadence, etc.
- although they can be modified temporarily, they are difficult to modify for a longer period of time
- based on behavioral traits
-
weaker
-
should be used in conjection w/ type 1–3 factors
-
“somewhere you are”
-
“something you can do”
-
“something you exhibit”
-
“someone you know”
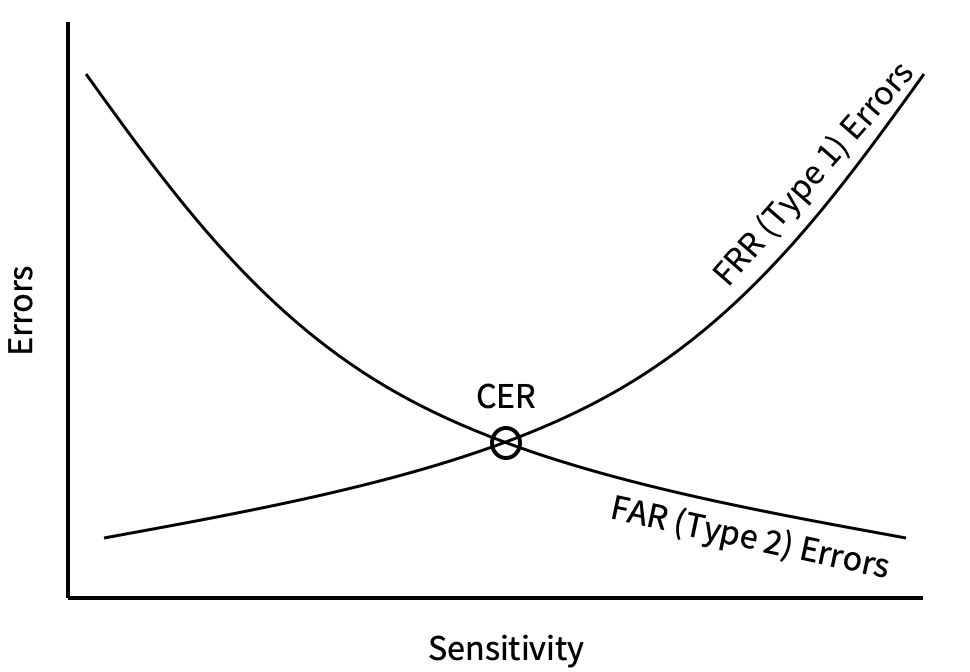
- false rejection
type I error- system fails to recognize an authorized user
- less serious
- results in loss of availability
- measured by false rejection rate (FRR)
- false acceptance
type II error- system misidentifies an individual as an authorized user
- serious error
- results in unauthorized indivduals have access to a system
- measured by false acceptance rate (FRR)
- crossover error rate
CER- FAR and FRR aren’t good measures on their own
- as the false rejection rate goes down, the false acceptance rate goes up, and vice versa
- FRR ↓ = FAR ↑, FRR ↑ = FAR ↓
- CER represents when an admin tunes a system to have an equal FAR and FRR value
- one time password generator — password is only used once, then is no longer valid
- reduces vulnerability to sniffing
- simple to implement (unless you’re a RAT)
- can be costly — hardware token expense
- users can lose or damage devices
- two types: synchronous or asynchronous
- synchronous
- synchronizes with an authentication server
- frequently based on time
- if damaged or battery dies, needs to by resynched
- asynchronous
- challenge-response
- user logs in
- authentication returns a challenge to the user
- user types the challenge into the device
- token returns a reply
- only a user’s token can respond with the expected reply
- more complex that sychronous
- may provide better protection against sniffing
- challenge-response
- synchronous
-
types
- physical token
- user presses a button to generate a code
- proves that they are in possession of the token
- physical token
-
soft token
- user retrieves code from app running on their phone
- alternative for users that don’t want to carry around a token
-
technology
- HOTP
HMAC-based one-time password- uses a shared secret and a counter
- creates a new code w/ each button press
- HOTP
-
TOTP
time-based one-time password- uses a shared secret and the time of day
- creates a new code every x seconds
-
static codes
- can be created to provide a backup to an MFA device
- dangerous
- users should be informed that these codes must be protected
- both are considered to be less secured
- phone numbers can be spoofed or stolen
- verify info stored on chip in the card
- more secure than memory cards
- can actually process information
- includes a microprocessor
- often integrated with PKI
- two types:
- contact
- contactless
- threats
- fault generation:
- manipulate environmental controls
- measure errors in order to reverse engineer logic
- side channel attacks:
- measure cards while they work (TEMPEST)
- differential power analysis: measure power emissions
- electromagnetic analysis: sample the frequencies emitted
- measure cards while they work (TEMPEST)
- microprobing
- remove outer protection of the card’s cicuits
- tap into ROM if possible
- “die” ROM to read data
- fault generation:
-
authentication mechanisms can be tricked
-
MFA combines two or more authentication techniques from two or more of the three authentication categories
-
provides a higher level of assurance
exam tip:
many pick biometric as the best authentication, but any one source can be compromised.
always look for more than one type. -
mutual authentication is beneficial
-
factors must be from different types
- i.e. a password and security questions are not MFA
- both are type 1 factors
look out!
look out for questions on the exam like this. - i.e. a password and security questions are not MFA
- client and server both know the password
- client sends username/password in plaintext
- not secure!
- offers no encryption
- must only be used w/in an encrypted channel
- client and server both know the password
- server sends a random challenge
- client computes a hash of the challenge + password
- client sends hash to the server
- server computes a hash of the challenge + password
- server compares it’s hash result w/ the hash result from the client
-
acceptible security
-
MS-CHAP and MS-CHAP2
- Microsoft-developed versions of CHAP
- both are insecure
both seek to reduce burden of IAM on users and admins
- XML (eXtensible Makrup Language)
- universal format for storing information
- SPML / SCIM (Service Provisioning Markup Lanuguage / System for Cross-domain Identity Management)
- XML-based formats for exchanging user and resource information and controlling provisioning
- SAML / OpenID (Security Assertion Markup Language)
- provides an XML-based framework for exchanging security-related info over networks
- individuals have accounts across multiple systems
- FIM systems share identity info
- reduces the number of individual identiees that a user must have
- shares a single authentication session across multiple systems
- avoids users needing to log in multiple times
- presents a single login screen then creates a session that persists across other systems
- session length can be length of a work day
- users will then only need to log in once at the beginning of their day
- allows for:
- reduction in user and IT frustration
- reduction of IT budget in managing disparate accounts
both provide a centralized approach to AAA
- first used for modem pools
- allows many apps to rely on the same authentication source
- example:
- a user wants to access a service
user → RADIUS client → RADIUS server → AD or LDAP - the user is either allowed or denied access
user ← RADIUS client ← RADIUS server ← AD or LDAP
or
user ← RADIUS client ← RADIUS server ← AD or LDAP
- a user wants to access a service
tip:
a RADIUS client is usually on an application server.
- disadvantages
- uses UDP, which is unreliable
- doesn’t encrypt the entire authentication sequence
- just the password
- one of the core protocols of Microsoft Active Directory
- ticket based authentication system
- network authentication protocol
- tries to ensure authentication security in an unsecure environment
- used in Windows 2K+ and some Unix flavors
- allows for single sign on
- never transfers passwords
- uses symmetric encryption to verify identifications
- avoids replay attacks
- main goal: users need to authenticate themselves without sending password over the network
- Authentication Server (AS): allows authentication of a user and issues a TGT
- Ticket Generating Ticket (TGT):
- Ticket Granting Service (TGS): after receiving a TGT from a user, the TGS issues a ticket for a particular user to access a particular service
- Key Distribution Center (KDC): a system that runs the TGT and AS
- ticket: means of distributing a session key
- principles: users, applications, services
- Kerberos software: integrated into most OSes. Win2K and up support it
-
user uses Kerberos client to provide username/password
-
user’s Kerberos client creates clear text authentication requests and sends to authentication server
-
authentication server looks up the user and retrieves the user’s password
-
authentication server sends two messages back to the client
- randomly generated session key
- used for future communication between the client and the ticket granting server
- encrypted using the client’s password
- ticket granting ticket
- includes
- info about client
- copy of the client’s TGS session key
- encrypted using a key known only to the ticket granting server
- includes
- randomly generated session key
-
client receives messages
- decrypts the first message using the user’s password
- gives it access to the client TGS session key
- if the user didn’t enter the correct password this step won’t work
- decrypts the first message using the user’s password
-
when client wishes to access a service, client contacts the ticket granting server and sends two things
- copy of the ticket granting ticket and identity of the requested service
- an authenticator
- containing:
- client’s ID
- current time
- encrypted using client TGS session key
- containing:
-
TGS receives messages
- decrypts the ticket granting ticket to retrieve the client TGS session key
- use the client TGS key to decrypt the authenticator and retrieve the client ID and timestamp.
-
TGS randomly generates a client server session key that the client will use to communicate with the desired service.
-
TGS then sends two messages back to the client.
- client server ticket
- encrypted using the services secret key
- contains the randomly generated client server session key
- copy of the client server session key
- encrypted with the client TGS session key
- client server ticket
-
client receives these two messages and is ready to complete the service authentication process
-
client sends two messages to the service * client server ticket that the client received from the ticket granting server * new authenticator encrypted with a client server session key
-
service receives these two messages * decrypts the first message to retrieve the client server session key * uses this key to decrypt the authenticator * validate the client granting access to the service.
- computers must have clocks synced within five minutes
- tickets stored on the workstation
- if the workstation is compromised, an identity can be forged
- if the KDC is hacked, security is lost
- a single KDC is a single point of failure and performance bottleneck
- still vulnerable to password guessing
lightweight directory access protocol
- means to query a centralized directory service such as LDAP
protocol port Kerberos 88 LDAP 389 LDAPS 636
-
previously used on Windows systems before Kerberos
-
depends on a hash-based challenge-response protocol
-
security issues
- weak encryption
- pass-the-hash
- allows use of credentials from one system to access another system
-
allows for SSO w/in a browser across different applications
-
three parties
- principal
- the user
- principal
-
identity provider
- org providing proof of identity
-
service provider
- org providing the web-based app that the user wants to use
- principal requests resource use from service provider
- service provider redirects to SSO page of the identity provider
- principal requests SSO from identity provider
- identity provider responds w/ XTML (SAML)
- principal requests assertion from service provider and provides SAML
- service provider redirects principal to service
- authenticated session may last for a period of time specified by the identity provider
- user doesn’t need to reauthenticate during this time
- provides a true SSO experience
- service provider uses identity providers authentication w/out gaining access to the user’s password
- password remains a shared secret between the user and the identity provider
- allows orgs to move IAM to the cloud
- example: OneLogin
- syncs w/ org’s existing on-prem or cloud-based directories to obtain info
- replaces authentication services for SaaS products
- simplifies user and admin experience
- IDaaS allow the use of MFA
- need to verify that IDaaS solution meets the org’s requirements for IAM
- need to conduct security review of the product
- related protocoles
- provide federated SSO for the web
- authorization protocol
- authentication protocol
-
digital certificates may be used for authentication
- contain a signed copy of a user’s/system’s public key
-
key-based authentication
- user create a key pair
- keep the private key
- provide the public key to the server
- user makes a connection request
- server creates a random challenge and sends to user
- user encrypts the random challenge w/ private key and send back to server
- server decrypts encrypted challenge w/ public key
- if a match, user is authenticated
- user create a key pair
-
CAs create digital certs for public keys used in authentication
-
cert authentication use
- SSH
- smartcards (CAC/PIV)
- network access (802.1x)
ability to trace every action back to a user
-
identification
- each user must have a unique identifier
- shared or generic accounts must not be used
- users can’t can’t say “I didn’t do it!”
-
authentication
- strong authentication prevents unauthorized individuals from gaining access
- prevents users from denying their activity
- users can’t claim “I was hacked!”
- systems must track user activity w/ auditing mechanisms
- logs must be secure
- admins or users could delete logs to cover tracks
- logs should be sent to a locked down centralized log server
-
should use timeouts and screensavers to disconnect users
-
timeouts
- disconnect user sessions after a predetermined time
- not user friendly
- disconnect user sessions after period of inactivity
- more user friendly
- require re-authentication to complete sensitive activited
- more user friendly
- disconnect user sessions after a predetermined time
-
screensavers
- common timeout mechanism
- locks machine and requires re-authentication to deactivate screensaver
-
implement least privilege
- least privilege
- users should only have minimum permissions necessary for their job function
- least privilege
-
implement separation of duties
- separation of duties
- sensitive functions should require action by two separate users
- separation of duties
-
implement job rotation
-
job rotation
- regularly move people between jobs to prevent fraud
-
mandatory vacations
- enforce periods when employees have no access to systems
-
manage account lifecycle
-
-
provisioning
- creating new users and granting permissions
-
job changes
- modify roles
- modify permissions
- recertification
- reviewing access on a regular basis and removing any unnecessary access
-
deprovisioning
- revoking permissions and deleting identities of terminated users
different account types require different access controls
-
user account
- accounts for normal users
- accountants, receptionists, HR, legal, etc.
- standard permissions
- standard monitoring
- accounts for normal users
-
privileged accounts
- accounts for completing admin functions
- server maintenance, changing object permissions, etc.
- shouldn’t be used for routine activities
- i.e. shouldn’t log in with admin account to complete a time sheet
- admin permissions
- strong controls for use
- monitor all actions
- accounts for completing admin functions
-
guest account
- should have a temporary lifetime
- limited permissions
- standard monitoring
-
shared account
- reduces accountability
- shouldn’t be used
-
service account
- provides access to internal server processes
- shouldn’t have interactive login rights
tip:
- all accounts should be used for a purpose
- avoid shared responsibility accounts
-
group policy
- used in Windows to apply configuration settings to users and computers
-
password policy
- most common authentication mechanism
- should be at least eight characters long
- should contain upper case, lower case, digits, special characters
- NIST guidance is that complex passwords should be allowed_, but not_ required
-
password expiration policy
- passwords should be required to be changed at a regular interval
- should guard against password reuse
- NIST guidance is that passwords should never expire
-
lockout policy
- lock out accounts after many incorrect login attempts
-
disablement
- unused accounts should be disabled
-
password recovery mechanisms
- allow users to reset passwords on a self-service basis
- relieves burden on help desk
- improves users satisfaction
- role
-
groups permissions to allow shared security settings
-
Windows security group
- implements role-based security
-
- simplifies account management
- admins can assign permissions to a new user by adding them to an existing role
- admins can remove permissions to a departing user by removing them from their role
- removes need to add new permissions to every account
- new permission can be added to role instead
- this cascades down to all users in the role
- replaces the need for shared accounts
protects against security incidents
- can block access needed for work (not enough access)
- can also violate least privilege (too much access)
- need to watch for privilege creep
used to ensure that users have accurate permissions
-
pull list of account permissions
-
reviews w/ management
-
makes adjustments as needed
-
pay attention to users that have switched jobs/roles
-
attestation
- formal approval of user permissions
-
unauthorized use
- illegal actions by legitimate users
-
should examine user, as well as system and service accounts
- system and service accounts shouldn’t have interactive login rights
- watch for suspicious activities
- alerts admins of anomolies
- things to look for
- impossible travel time logins
- unusual network location logins
- unusual time-of-day logins
- deviations from normal behavior
- deviations in colume of data being transferred
- geotagging
- tags logs w/ user location
- geofencing
- alerts admins if devices leave pre-set boundaries
safeguard admin accounts
-
password vaulting
- store admin password
- may remote into a server w/ admin account username and password
- prevents owner of admin account from even knowing password
- may provide just-in-time access
-
command proxying
- eliminates need for direct server access
- PAM system sends commands to services/servers as the admin account
-
monitoring
- logs admin account activity
-
credential management
- rotates passwords and keys
-
PAM solutions will need to provide emergency access workflows
-
sudo(super user do)- allows users to temporarily assume admin rights
- use should be minimized
-
after onboarding
- creates authentication credentials
- grants appropriate authorizations
-
workflow should be established for internal job transfers as well
-
should avoid privilege creep
- privilege creep
- users accumulate privileges when transferring jobs/roles
- violates least privilege
- privilege creep
- during offboarding
-
disables accounts
-
revokes access at appropriate time
-
prompt terminations is critical
- prevents users from accessing resources w/o permission
- critical when user leaves under adverse circumstances
-
- routine workflow
- disables accounts on a routine basis
- used for planned departures
- emergency workflow
- immediate suspension of access
- used for unexpected departures
- timing is critical!
- too early, may inform of impending termination
- too late, may allow access to resources afrter termination
final step in granting access to a resource or system
-
authorization is ensuring that someone who is authenticated is allowed to access a resource
- authorization is a preventative control
-
OSes and applications can provide authorization functionality
-
authorization can be based on:
- user
- groups
- roles
- rules
- temporal isolation: time of day
- transaction type
- users should only have minimum permissions necessary for their job function
- limits damage from insider attacks
- users only have permissions for limited number of things
- limits damage from external attacks
- stolen accounts only have permissions to do a limited number of things
- no individual should possess permissions that when combined allow them to perform a highly sensitive action
- ex. accountant creating a new vendor and cutting checks to that vendor
exam tip:
be able to identify least privilege and separation of duties if given a scenario.
- users accumulate privileges when transferring jobs/roles
- violates least privilege
- auditing can help mitigate
- RBAC can defend against creep
- limit privilege creep
- can be automated or manual
- controlling a subject’s access to an object
- controls assignment of rights/privleges to accounts
- Per (ISC)², IAM solutions:
“focus on harmonizing the provisioning of users and managing their access across multiple systems with different native access control systems.”
- OS restricts authorizations
- based on labels on users and objects
- OS compares labels on users and objects and decides if user can make requested actions
- users are not allowed to change authorizations
- rarely used in production environments
- most common example is SELinux
-
resource owners set DAC permissions using ACLs
-
table of usernames and permissions grants to each user
-
NTFS example permissions
- full control: permission to do anything
- read: read a file (duh)
- read and execute: read files and execute executable files
- write: write changes to a file
- modify: write and delete permission
-
SQL Server authentication
- use local database accounts
-
Windows authentication
- use host Windows server user accounts
-
Mized authentication
- use both SQL server and Windows server accounts
-
most other databases can use similar database-based and OS-based authentication
- manages permissions through roles assigned to users by admins
- manages permissions by admins granting explicit permissions to each account
- any action not explicitly allowed must be denied
- firewalls are the best example of this principle
- permissions are grouped together in functional roles
- users are assigned to those roles
- admins make access control decisions
- based on characteristics of a user/object/environment
- allows for conditional access conditions
- limits access based on geographical locations
- i.e. you can’t log into the VPN from Iran
- limites access based on login time
- i.e. receptionists can’t login during the weekends
-
manipulates people
- diverging sensitive info
- performing an action that undermines security
-
uses several psychological factors:
- authority and trust
- people defer to authority
- authority and trust
-
intimidation
- scaring people
-
consensus / social proof
- herd mentality
-
scarcity
- getting the last one
-
urgency
- time is running out
-
familiarity / liking
- people will say yes to people that are likeable
-
education is the solution to social engineering attacks
- come in many forms
-
unsolicited email
-
phishing
-
spam iliciting info
-
often used in recon stage of an attack
-
spear phishing
- targeted attacks on certain invidivuals
- usually have higher success rates
-
invoice attacks
- send fake invoices to accounting and payment departments
- hope that fake invoice is inadvertently paid
* whaling - target senior executives
- often use fake subpoenas
-
-
prepending attacks
- [INTERNAL / SAFE] impersonate security filters on email systems (just like that)
- use fake websites
- typosquatting allows for user confusion
- often used in conjunction w/ phishing or DNS poisoning
- voice phishing
- watch Kitboga on Twitch
- SMS and IM phishing
-
faking an identity
-
as with social engineering, education is key
- targets an individual
- attempts impersonate individual to gain access to accounts, funds, etc.
- series of steps taken to impersonate
- attacker contacts various agencies and orgs in an attempt to gain access
- combine info known about the user as well as security questions
- attempt to gain a foothold in one system to springboard into others
- difficult to defend against
- requires security at every step
- strong authentication procedures provide protection
-
websites can effectively spread malware
- users usually trust a website
- browser add-ons can often have vulnerabilities
- users are conditioned to not read popups or alerts
-
steps
- attacker identifies and compromises popular website
- attacker chooses a client exploit and bundles in a botnet
- attacker places malware on website
- attacker waits for infected systems to “phone home”
-
limitations
- attackers can’t just build a website
- have to use popular website
- content filters can often block malicious material
- attackers can’t just build a website
-
watching someone’s screen
-
solutions
- be aware of surroundings
- use screen filters
-
digging through the trash
-
solution
- shred sensitive documents
- shred everything
- can still be recycled
- Bob will pick it up for you
- shred sensitive documents
-
slipping in behind someone
-
solutions
- anti-tailgating policy
- turnstiles
- data flow between a subject and an object
- subject is active — person, process, program
- object is passive — file, database, printer
- access controls: security mechanisms than control how a subject can interact with objects
- access controls should:
- support the CIA triad
- regulate what a subject can do to an object
- be layered
- provide both proactive and reactive protection
- access controls should: